Basic server-side template injection (code context)
Description
This lab is vulnerable to server-side template injection due to the way it unsafely uses a Tornado template. To solve the lab, review the Tornado documentation to discover how to execute arbitrary code, then delete the morale.txt file from Carlos’s home directory.
Reproduction and proof of concept
Log in as
wiener:peterand while proxying traffic through Burp, log in and post a comment on one of the blog posts.Notice that on the My account page, you can select whether you want the site to use your full name, first name, or nickname.
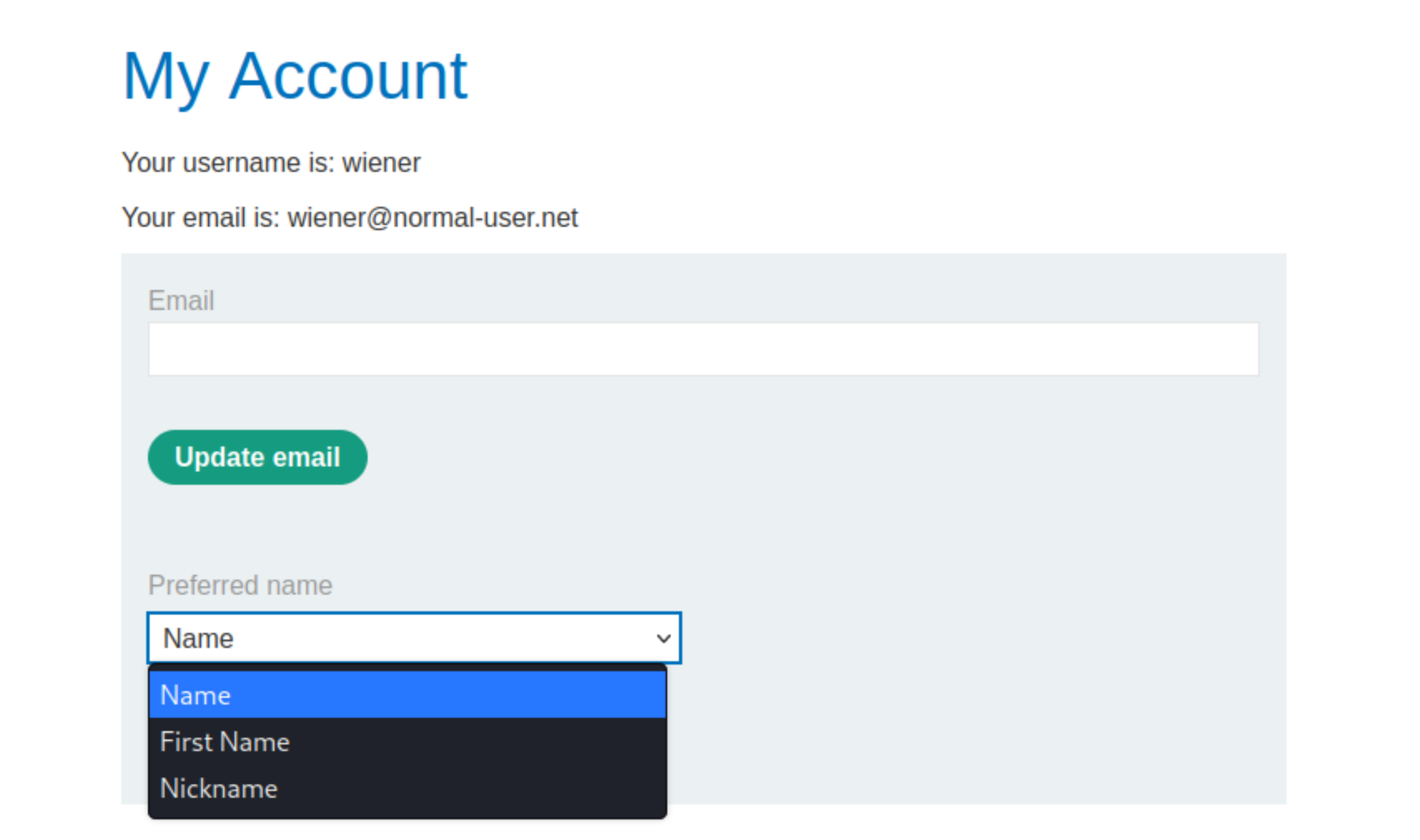
When you submit your choice, a POST request sets the value of the parameter blog-post-author-display to either user.name, user.first_name, or user.nickname. When you load the page containing your comment, the name above your comment is updated based on the current value of this parameter.
In Burp, go to Proxy” > “HTTP history and find the request that sets this parameter, namely
POST /my-account/change-blog-post-author-display, and send it to Burp Repeater.Study the Tornado documentation to discover that template expressions are surrounded with double curly braces, such as
{{someExpression}}. In Burp Repeater, notice that you can escape out of the expression and inject arbitrary template syntax as follows:
blog-post-author-display=user.name}}{{7*7}}
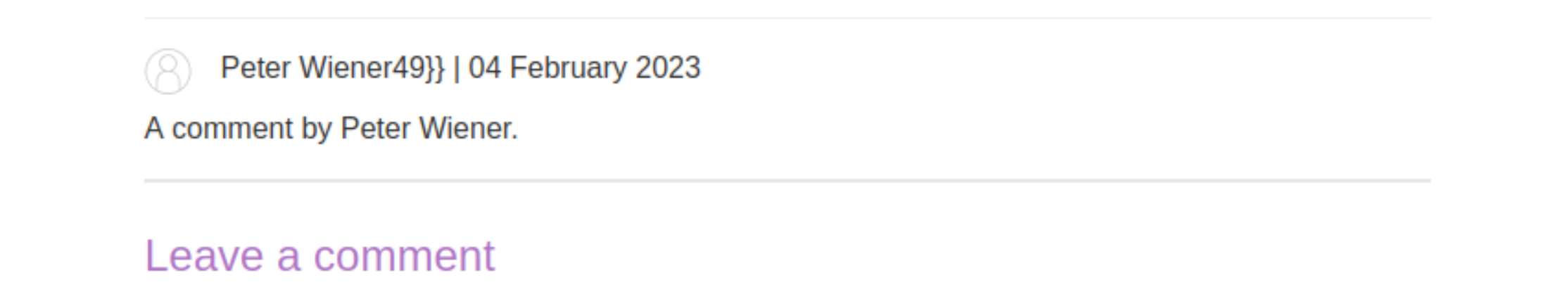
Reload the page containing your test comment. Notice that the username now says
Peter Wiener49}}, indicating that a server-side template injection vulnerability may exist in the code context.
In the Tornado documentation, identify the syntax for executing arbitrary Python:
{% somePython %}
Study the Python documentation to discover that by importing the
osmodule, you can use thesystem()method to execute arbitrary system commands.Combine this knowledge to construct a payload that deletes Carlos’s file:
{% import os %}
{{os.system('rm /home/carlos/morale.txt')
In Burp Repeater, go back to
POST /my-account/change-blog-post-author-display. Break out of the expression, and inject your payload into the parameter, remembering to URL-encode it as follows:
blog-post-author-display=user.name}}{%25+import+os+%25}{{os.system('rm%20/home/carlos/morale.txt')
Reload the page containing your comment to execute the template and solve the lab.
Exploitability
An attacker will need to review the Tornado documentation to discover how to execute arbitrary code, then log in and delete the morale.txt file from Carlos’s home directory.